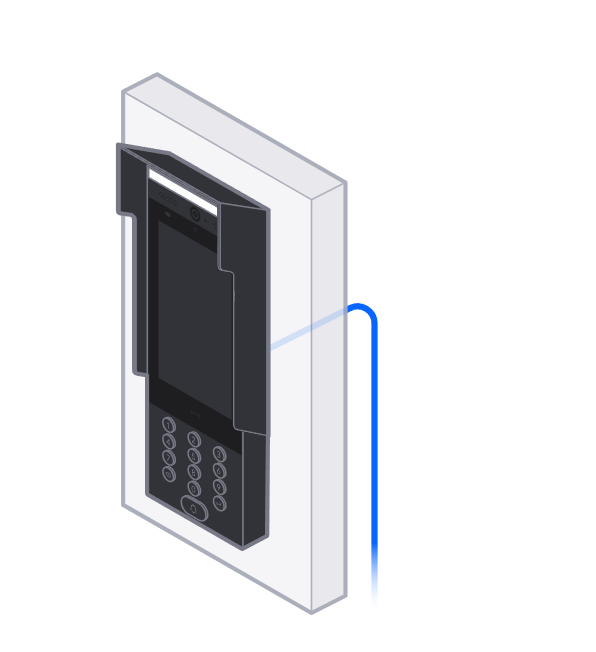
Ubiquiti UniFi Access G2 Pro
Our preferred video intercom for luxury residential and commercial entry — HD camera, NFC, PIN, two-way audio, and native UniFi platform integration.
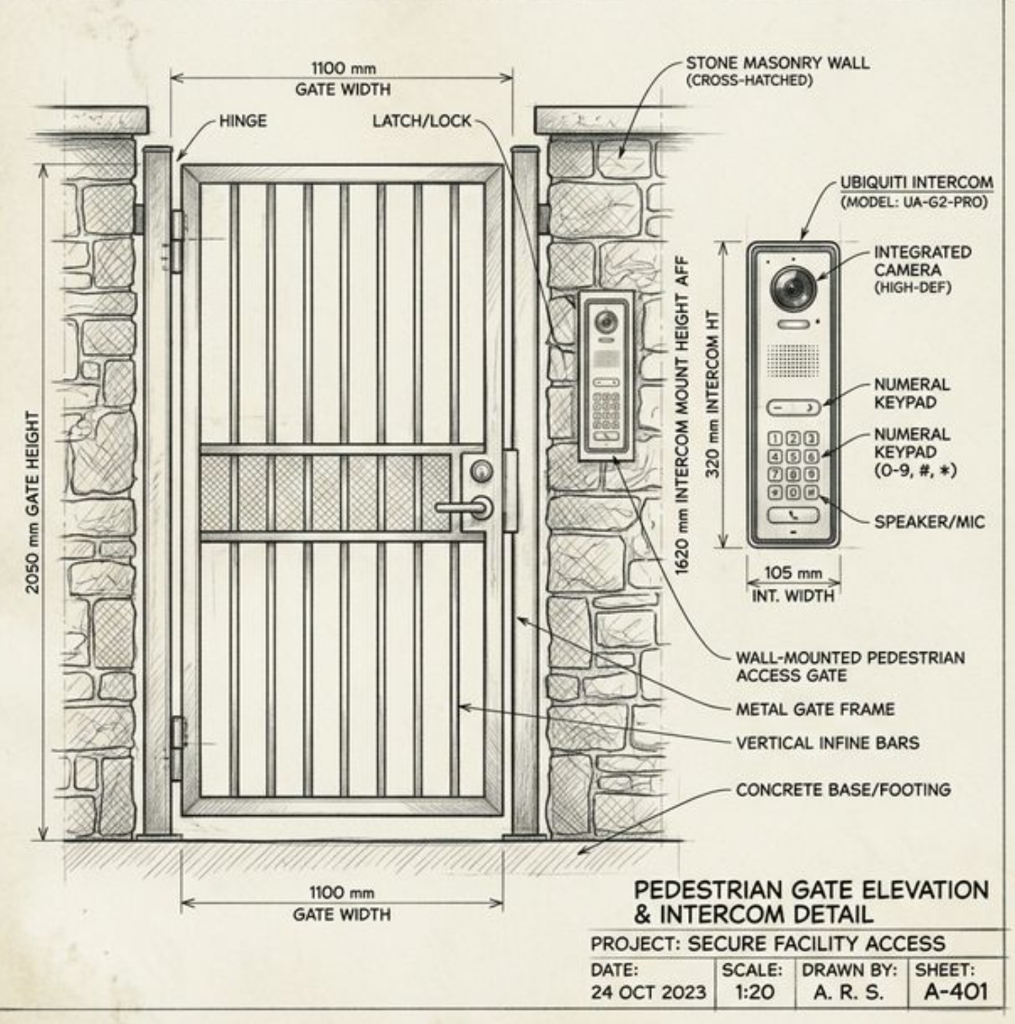


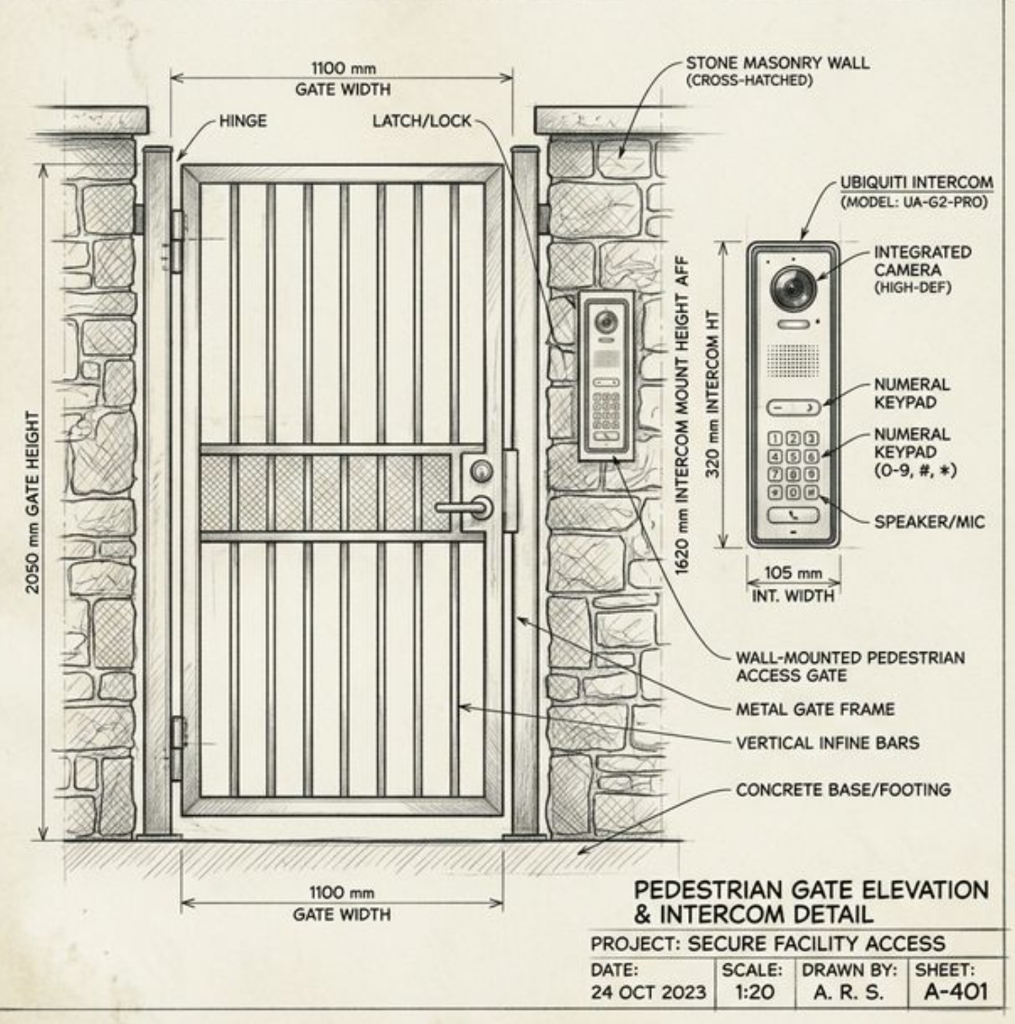
From gated estate driveways to penthouse elevator lobbies — we design, document, and install access control systems with the same engineering rigor as your core automation infrastructure.
From the front gate to the elevator penthouse key — every entry point documented, engineered, and installed to the same standard as the rest of your system.
Ubiquiti UniFi Access G2 Pro, 2N, and Aiphone systems with HD camera, two-way audio, NFC, and PIN access — fully integrated with your smartphone and automation platform.
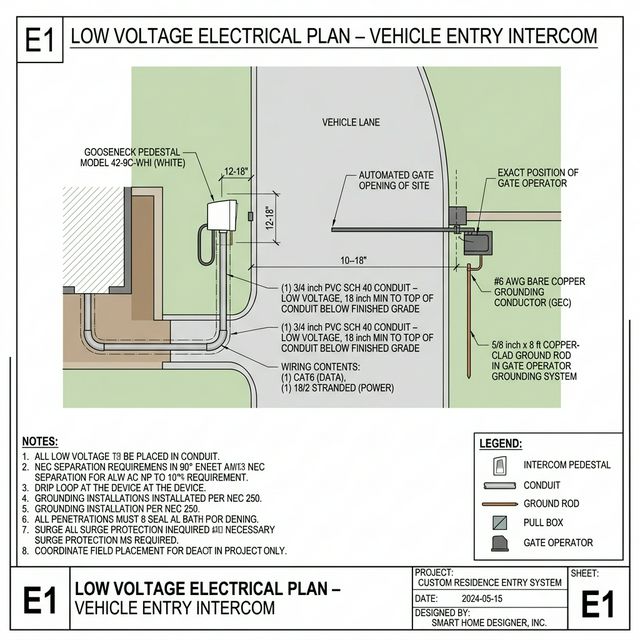
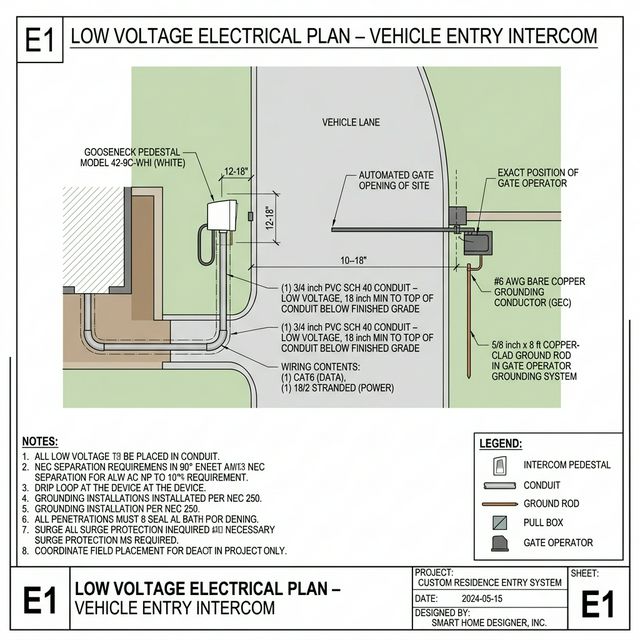
→ Ubiquiti · 2N · AiphoneMotorized gate operators with gooseneck intercom pedestals, vehicle loop detectors, UPS backup, and NEC-compliant low-voltage wiring — complete driveway entry solutions.
→ LiftMaster · FAAC · ApolloCredential-based access with NFC fobs, key cards, and PIN keypads at every entry point. Role-based access levels, audit logs, and remote lockout capability built in.
→ Ubiquiti UniFi Access platform4K IP camera systems integrated with your network — concealed tree/wall mounts, custom-painted hardware to match the environment, and full NVR/cloud recording.
→ Ubiquiti · Axis · HanwhaNEC-compliant conduit routing, as-built E-series electrical plans, permit-ready documentation and shop drawings — every installation fully documented before we pull wire.
→ E1 plans · permit packages · as-builtsAccess events trigger your automation system — arrival locks unlock and sets the "Welcome" scene, departure arms the system and closes the gate. One integrated experience.
→ Crestron · Control4 · Lutron RA3Our preferred video intercom for luxury residential and commercial entry — HD camera, NFC, PIN, two-way audio, and native UniFi platform integration.


We specify commercial-grade equipment rated for luxury residential demands — not off-the-shelf consumer hardware.
Entry events trigger whole-home scenes, lighting, and HVAC automatically
Unlock gates and doors remotely from anywhere via UniFi app or Crestron
Complete access history — who entered, when, and via what credential
UPS backup, fail-secure/fail-safe logic, and redundant credential paths
Every property is different. We'll assess your entry points, design the right hardware and documentation package, and deliver a system your contractor can build from.
Tell us about your property, entry points, and security goals.